

The authenticated encryption of HTTPS similarly protects the CDN-based web clock approach. This avoids situations where an attacker-in-the-middle tampers with insecure NTP responses, messing up your system’s clock.
Almost… there is this fun thing called a delay attack that works despite encryption! (I’ll admit that it’s probably not a practical concern.)
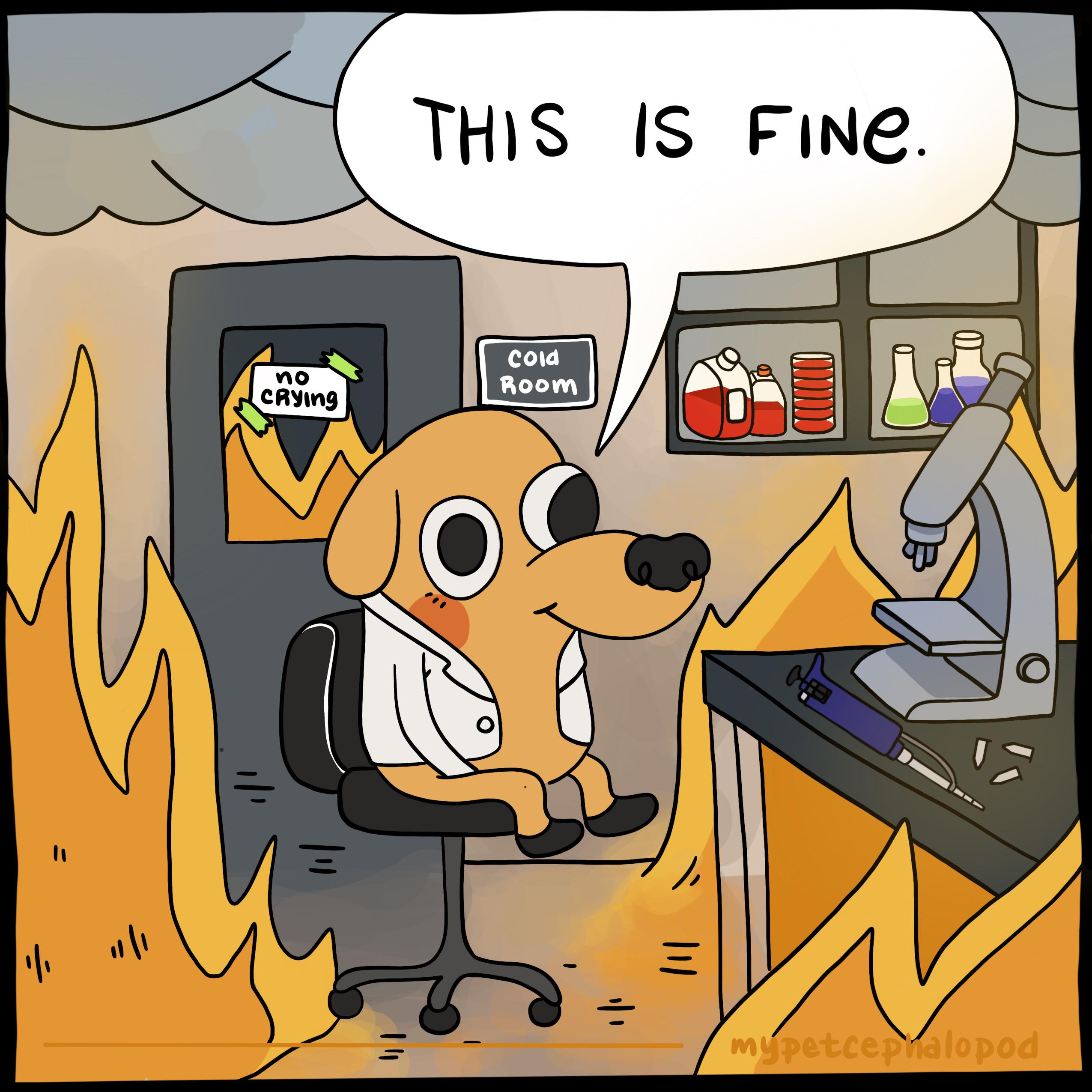
Anyway, the article talks about time measurements through an absurd amount of abstraction layers. Please don’t ever call this “simple” or even “cloud-native time” or the like.
If you start trying to improve this setup you’ll find so many face-palm moments. Like TCP retransmissions (which the article mentions, to be fair). You’d have to use WebRTC to avoid that, which I bet the CDN network doesn’t support. Or the fact that web browser timers have intentionally reduced precision to resist fingerprinting. (Granted, if you are still in the milliseconds range it is not a problem.)









It’s cute how they think they can control every technology by controlling commercial sales. And this after 3D printing started as this huge RepRap movement where everybody and their friend built their 3D printer from online instructions and rollerblade bearings.
Up next: when buy a 3D printer kit, you have to agree to only flash the unmodified firmware on your Arduino, and not one of the forks from Github. And you are no longer allowed to create your own hardware at home, or tinker with electronics of any kind, or publish instruction how to make your own electronics. And after that, you now need to register yourself before you can use a debugger.